Trezor Login: The Gateway to Secure Crypto Access
Your ultimate guide to Trezor login — from connecting your device to verifying your digital identity. Keep your assets safe while staying in control.
What Makes Trezor Login Unique?
Logging in with Trezor isn’t just convenient — it’s a complete redefinition of security. Forget passwords and phishing risks. With Trezor’s hardware-based login, your private keys never leave your device, ensuring your crypto is always protected by physical confirmation.
Hardware-Backed Login
Trezor uses your hardware wallet as your identity key. Each login is confirmed by cryptographic proof, making it impossible for hackers to impersonate you.
Zero Password Fatigue
No more password resets or forgotten logins. Your Trezor device acts as the universal key to all your compatible accounts.
Phishing-Proof Design
Even if someone tricks you into a fake site, your Trezor won’t approve it unless the domain matches exactly. It’s login, evolved.
Login Flow: Simplified Example
// 1. Connect Trezor device
const trezor = await connectDevice();
// 2. Request login verification
const challenge = await server.createChallenge();
// 3. Sign challenge via hardware wallet
const signature = await trezor.signChallenge(challenge);
// 4. Verify login
const verified = server.verifySignature(signature);
if (verified) grantAccess();
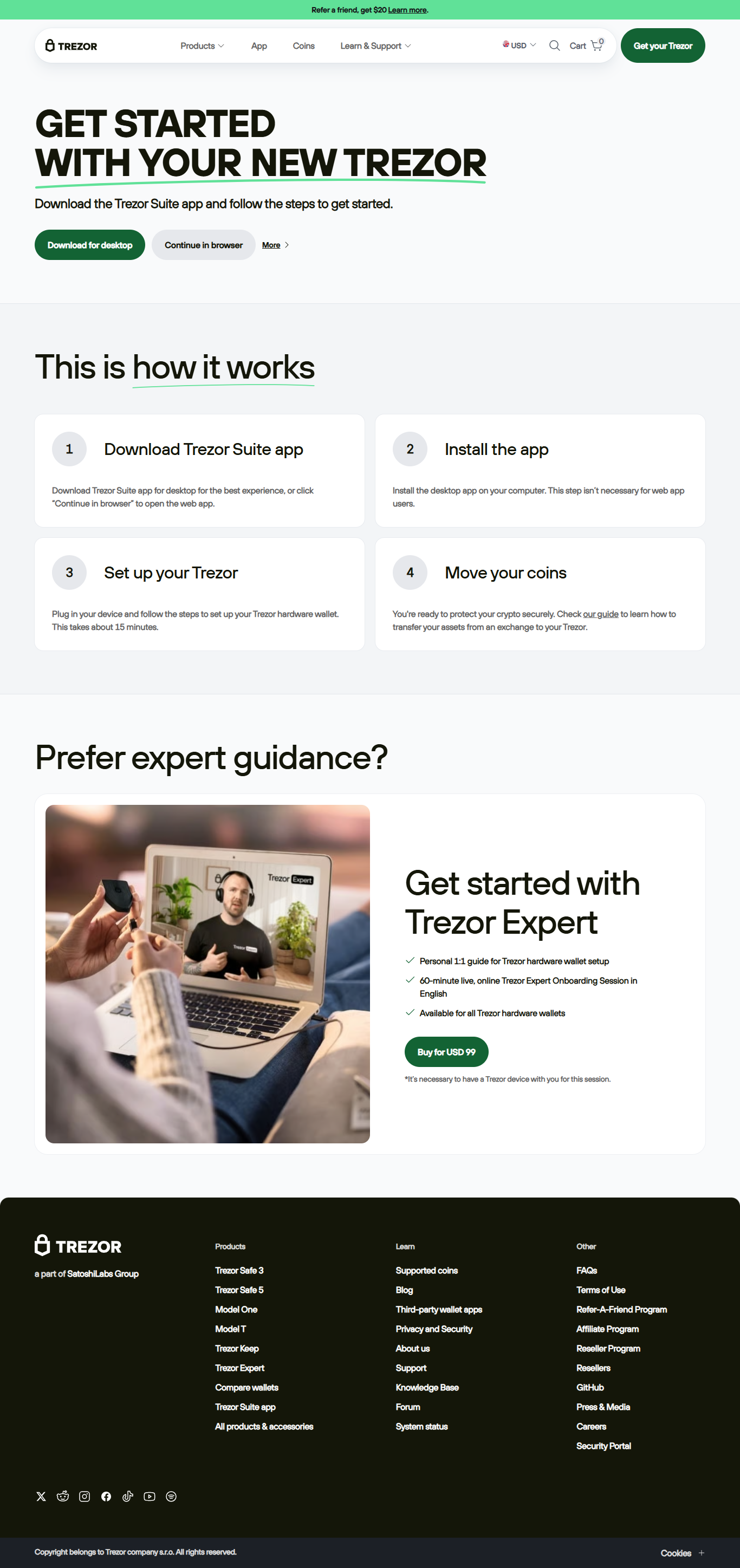
How to Log In Using Trezor
Go to trezor.io/start or open Trezor Suite on your computer.
Connect your Trezor device via USB or cable and unlock it with your PIN.
Approve the login request shown on your Trezor device screen after verifying the website name.
Access your wallet dashboard or dApp instantly without typing a password.
“Your Login Is Your Hardware.”
Trezor’s login model replaces digital passwords with physical proof. No online system can ever copy your hardware key — only you can approve access, right from your fingertips.
Trezor Login vs Traditional Login
Trezor Login — FAQ
A: Only sites supporting WebAuthn or hardware authentication currently allow Trezor login, but the list keeps growing.
A: You need it for the app or site to communicate with your Trezor Suite, but your keys remain offline throughout the process.
A: You can restore your access using your recovery seed phrase on a new device. Always keep it safe and offline.
Secure Your Digital Life with Trezor Login
With Trezor Login, your identity lives in your hands — literally. No passwords. No hacks. Just pure, verified, cryptographic trust.